Yearn Finance Exploit Points to Dangers of Old Smart Contracts

DeFi stalwart Yearn Finance was the target of a dizzyingly complex attack early Thursday that resulted in a roughly $11.6 million stablecoin haul for the culprit.
But the root cause dates back over three years, to a version of the savings protocol that has long since been officially abandoned.
At least $8 million in stablecoins remains in the hacker’s control, most of which has been swapped to DAI, with the remaining millions exchanged for ether (ETH) and partially passed to crypto mixer Tornado Cash in an effort to obfuscate its origin.
Yearn’s YFI governance token initially fell by roughly 5% on the news, but remains up nearly 80% year-to-date, data from CoinGecko shows.
Yearn’s official Twitter confirmed the exploit, noting that the affected vault is “an immutable contract predating YFI, [that] was deprecated in 2020.”
The attacker was able to take advantage of a vulnerability in the deployment of one of the early Yearn vaults involving tether (USDT) deposits, which receive a Yearn-equivalent token yUSDT, according to security researchers Otter Sec, samczsun and Peckshield.
Using starting capital of just 10,000 USDT, the perpetrator was able to mint over 1.2 quadrillion yUSDT and then swap those for other stablecoins via Curve Finance to extract a total of $11.6 million.
It appears the root cause is due to the misconfigured yUSDT, which is exploited to mint huge yUSDT (1,252,660,242,212,927.5) from a small $10K USDT. The huge yUSDT is then cashed out by swapping to other stable coins. https://t.co/Qz3vwtbcot pic.twitter.com/xlsc2Nlmle
— PeckShield Inc. (@peckshield) April 13, 2023
The attack vector is linked to an apparent oversight from February 2020, when the yUSDT token contract was deployed with a bug.
It seems like the iearn USDT token (yUSDT) has been broken since deploy, which was *checks notes* over 1000 days ago. It was misconfigured to use the Fulcrum iUSDC token instead of the Fulcrum iUSDT token.https://t.co/FMtjACkGNz pic.twitter.com/dxW9E0ndF1
— samczsun (@samczsun) April 13, 2023
The detail identified by Samczsun regarding an apparent “misconfiguration” is notable, according to Ernesto Garcia, Smart Contract Engineer at OpenZeppelin.
“It seems weird to me that the Fulcrum iUSDC address is hard-coded,” Garcia told Blockworks. “If the contract went through a review, it was either an oversight (everyone assuming the correct address), or might’ve been changed before deployment as some tweets out there suggest.”
Garcia suggested that bytecode verification against the audited code from the time would determine whether there was any deliberate tampering.
Aside from the age of the bug, the execution of this attack required multiple steps, three different DeFi protocols, including Aave and a flash loan.
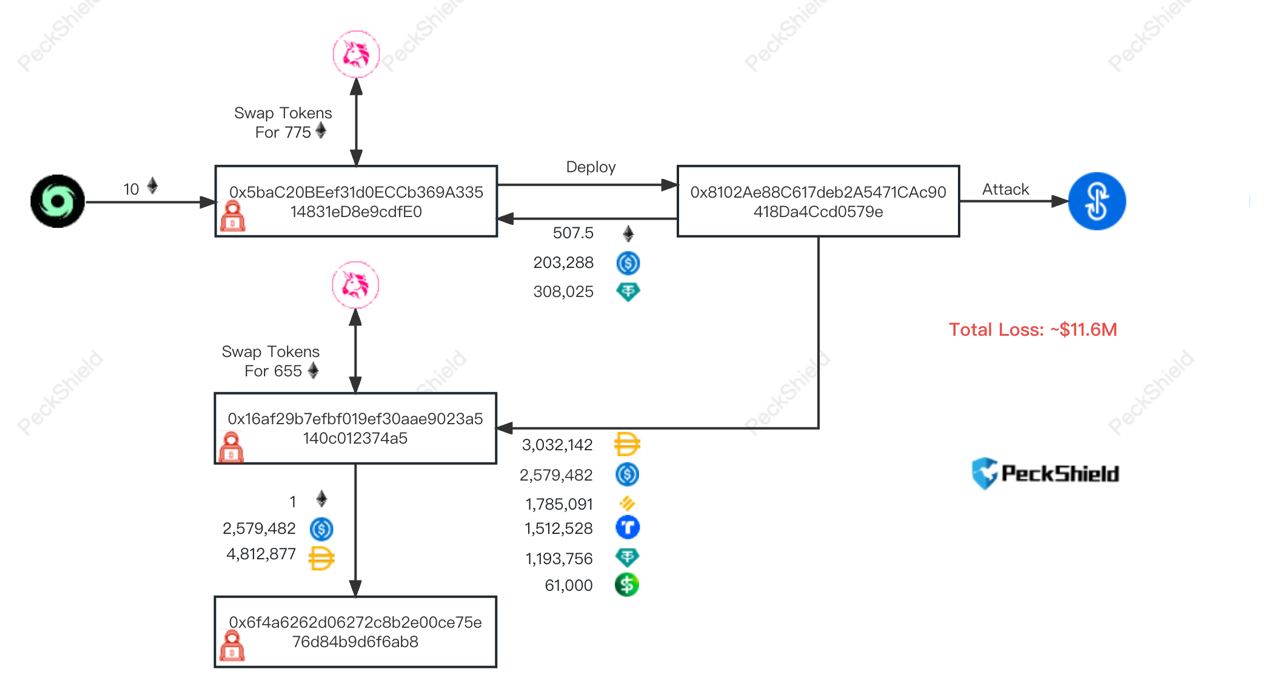
Diagram of the flow of funds; Source: Peckshield
Aave itself is unaffected, meaning its users are not at risk, according to Peckshield, nor are users of more recent Yearn vaults.
The unknown attacker converted $1.2 million USDT to 621 ETH, and used exploited TUSD stablecoin as collateral in Aave V2 to borrow a further 320 ETH ($640,000). Much of that ether has been deposited into the Tornado Cash 100 ETH anonymity set, blockchain records show.
A separate wallet linked to the first received over 4.7 million DAI and 2.5 million USDC, with the latter swapped to DAI, where it remains as of 9:30 am ET.
Hackers prefer DAI and ETH over USDC and USDT because the centralized stablecoins from Circle and Tether are more easily frozen, preventing further transfer.







 Bitcoin
Bitcoin  Ethereum
Ethereum  Tether
Tether  USDC
USDC  Dogecoin
Dogecoin  Cardano
Cardano  Chainlink
Chainlink  TRON
TRON  Bitcoin Cash
Bitcoin Cash  Polygon
Polygon  Litecoin
Litecoin  LEO Token
LEO Token  Dai
Dai  Ethereum Classic
Ethereum Classic  Hedera
Hedera  Cosmos Hub
Cosmos Hub  Stellar
Stellar  Cronos
Cronos  OKB
OKB  Monero
Monero  Stacks
Stacks  Maker
Maker  Theta Network
Theta Network  EOS
EOS  Algorand
Algorand  Gate
Gate  NEO
NEO  KuCoin
KuCoin  Synthetix Network
Synthetix Network  Tezos
Tezos  IOTA
IOTA  Bitcoin Gold
Bitcoin Gold  Tether Gold
Tether Gold  TrueUSD
TrueUSD  Enjin Coin
Enjin Coin  0x Protocol
0x Protocol  Zilliqa
Zilliqa  Holo
Holo  Zcash
Zcash  Ravencoin
Ravencoin  Siacoin
Siacoin  Qtum
Qtum  Basic Attention
Basic Attention  Dash
Dash  NEM
NEM  Decred
Decred  Ontology
Ontology  Waves
Waves  Lisk
Lisk  DigiByte
DigiByte  Numeraire
Numeraire  Nano
Nano  Pax Dollar
Pax Dollar  Status
Status  Hive
Hive  Steem
Steem  OMG Network
OMG Network  Huobi
Huobi  BUSD
BUSD  Ren
Ren  Bytom
Bytom  Kyber Network Crystal Legacy
Kyber Network Crystal Legacy  Bitcoin Diamond
Bitcoin Diamond  Energi
Energi  Augur
Augur  HUSD
HUSD